Azure KeyVault – RBAC as a security best practice. For those who are new to this, I hope this essay will guide you in authorizing access to Azure KeyVault.
In KeyVault, there are currently two methods for specifying access to the data plane (secrets, certificates, and keys). Please see the table below:
| Feature | Access policy | RBAC |
|---|---|---|
| Grant access to secrets/certificates/keys | yes | yes |
| Grant access to specific secret/certificate/key | no | yes |
| Use groups | no | yes |
| Use Privileged Identity Management (PIM) | no | yes |
| Deny assignments | no | yes |
| Centralized access management for administrators | no | yes |
| Use the same API for Azure services | no | yes |
As you see, almost every useful feature is available in the RBAC. For example, if you have an application that needs to read one secret, you can only give access to all the secrets. Do you see my point? This app requires one, but you give them access to 100 secrets!
We determined that RBAC is a superior strategy for granting access. Let’s have a look at how to do so with Terraform. If you’re familiar with Terraform, you can get to the sources here. Enjoy!
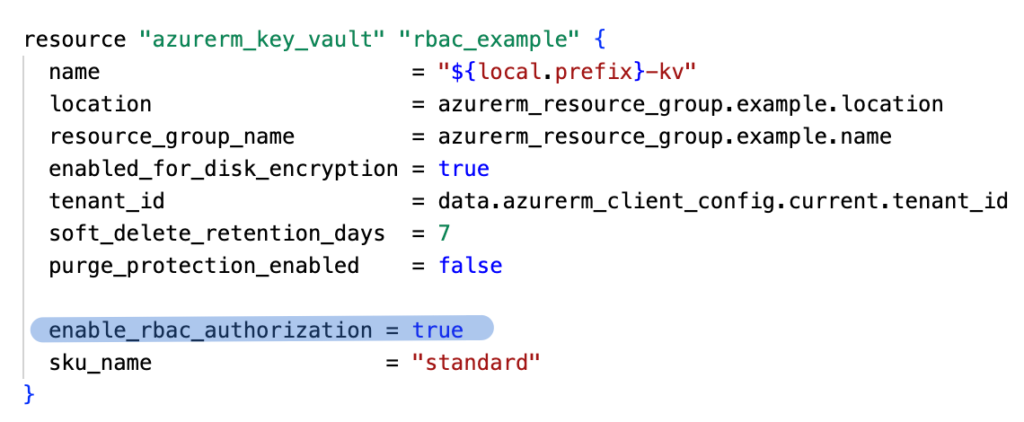
First step, create KeyVault, with RBAC authorization enabled:
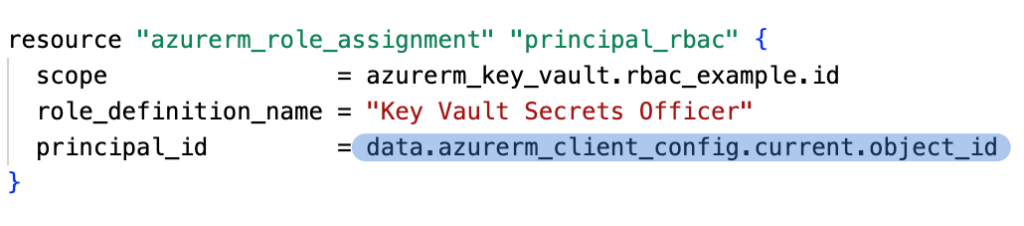
Next step: Add permission for the current user to add a secret:
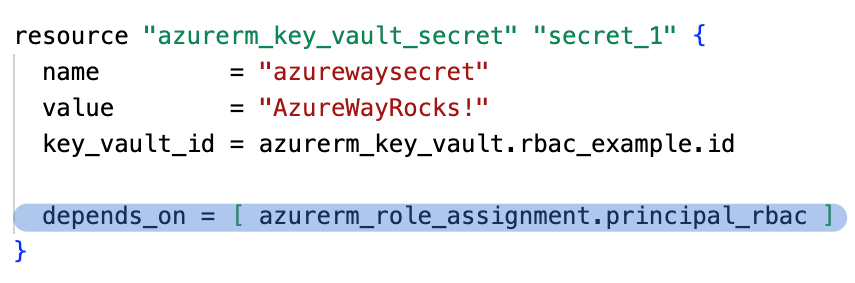
We can add a new secret in the KeyVault, pay attention to the depends_on block. We must add it because we don’t have a direct reference to the role assignment, without it our execution will fail due to lack of permission.
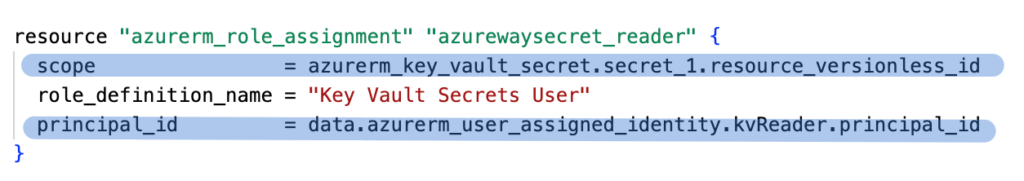
We have a secret in the KeyVault, so we can add permission for it. Again, pay attention to the scope argument (resource_versionless_id) and principal_id (user for which permission is. granted).
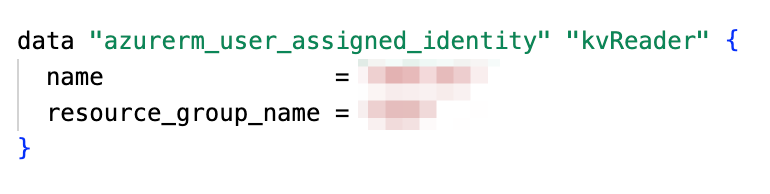
In my example, I’m using User Managed Identity, which I obtained using below code:
Remember that your account, in which context you execute Terraform, needs to have Owner permission on the Resource group or Subscription. Without the owner’s permission, you cannot assign roles.
In the documentation, you can find all defined roles for the Azure KeyVault data plane: https://learn.microsoft.com/en-us/azure/key-vault/general/rbac-guide?tabs=azure-cli#azure-built-in-roles-for-key-vault-data-plane-operations

Great article! You’ve done an excellent job explaining the essentials of using Azure Key Vault. It’s a powerful tool for securing secrets, and your breakdown really highlights its benefits.
Coincidentally, I recently wrote a post on a similar topic, focusing more on best practices for managing secrets securely in .NET Core. If you’re interested, feel free to check it out here [****]. Keep up the great work!
Great article promoting security best practices.